
How to Protect Cloud Data From Unauthorized Access
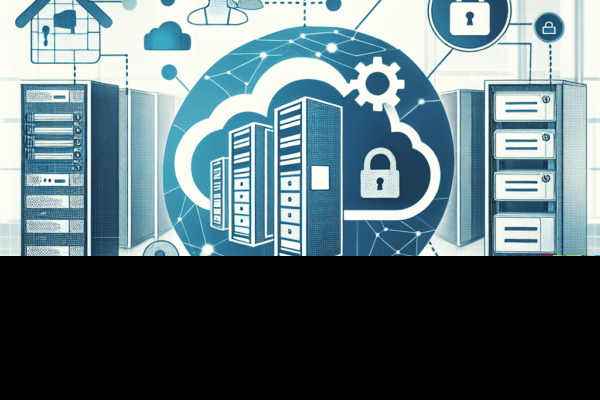
Enterprises migrating critical workloads to the cloud demand a comprehensive approach to safeguard sensitive information from unauthorized infiltration. Effective strategies…

Enterprises migrating critical workloads to the cloud demand a comprehensive approach to safeguard sensitive information from unauthorized infiltration. Effective strategies…

Effective access control is at the heart of any comprehensive business security strategy. Organizations that fail to implement strong and…
Securing organizational assets has never been more critical as threat actors evolve their tactics daily. Businesses of all sizes must…

Protecting a company’s sensitive information is not merely an IT concern; it is a critical aspect of overall business security….

Effective communication channels are central to sustaining a competitive edge and maintaining stakeholder trust. Protecting sensitive data as it traverses…

Managing the influx of connected devices in a corporate environment demands a strategic approach that goes beyond standard IT protocols….

As organizations navigate an increasingly interconnected world, company leaders must recognize the pivotal role of robust cybersecurity in protecting assets,…

Businesses around the globe face an escalating array of digital threats that demand robust solutions to safeguard sensitive information. Implementing…

The relentless advancement of cyber threats has compelled enterprises to rethink traditional perimeter defenses, propelling Zero Trust Architecture into the…
How to Securely Share Files Within Your Organization is a critical topic in the realm of business security, especially as…