
How to Secure Legacy Systems in Modern Environments
Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…

Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…

Managing access for a distributed team requires a strategic approach that balances usability with ironclad protection. As organizations embrace flexible…

Securing APIs in business applications involves a multi-layered approach that addresses potential vulnerabilities at every stage of development and deployment….

Enterprises migrating critical workloads to the cloud demand a comprehensive approach to safeguard sensitive information from unauthorized infiltration. Effective strategies…

Effective access control is at the heart of any comprehensive business security strategy. Organizations that fail to implement strong and…

The relentless advancement of cyber threats has compelled enterprises to rethink traditional perimeter defenses, propelling Zero Trust Architecture into the…
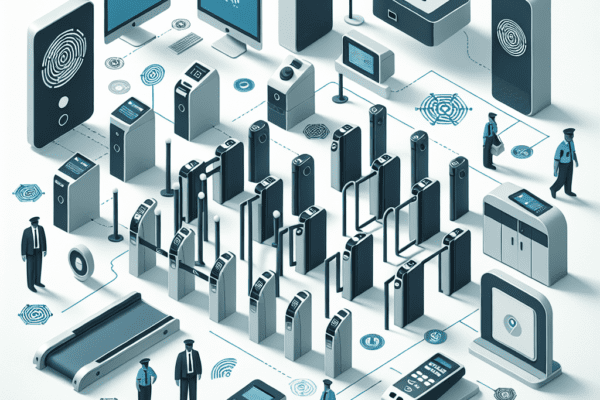
The role of physical access control in security is a critical aspect of safeguarding assets, information, and personnel within an…