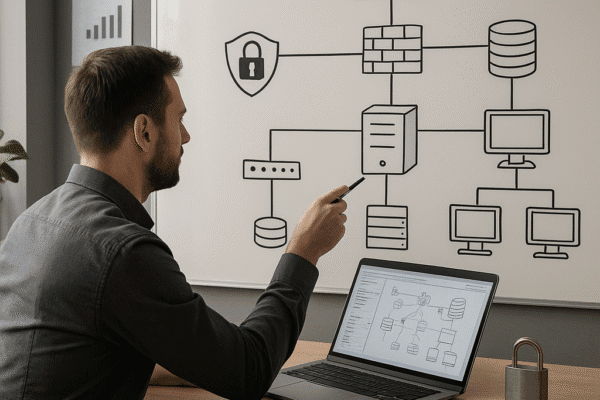
How to Design a Secure IT Infrastructure
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…
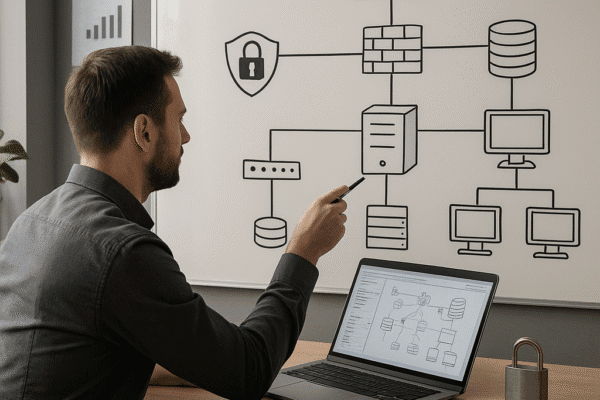
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

Effective data encryption is a cornerstone of robust business security strategies, ensuring that sensitive information remains protected from unauthorized access….

Enterprises migrating critical workloads to the cloud demand a comprehensive approach to safeguard sensitive information from unauthorized infiltration. Effective strategies…

Protecting sensitive information is a critical aspect of modern business operations. Data leakage can undermine a company’s reputation, financial stability,…

The Role of Encryption in Data Security explores how modern organizations protect sensitive information against evolving threats. Effective encryption strategies…

The role of encryption in business data protection is crucial in an era where cyber threats are increasingly sophisticated and…