
How to Build a Cyber-Resilient Organization
Building an organization capable of withstanding and recovering from cyberattacks hinges on a strategic blend of technology, processes, and people….

Building an organization capable of withstanding and recovering from cyberattacks hinges on a strategic blend of technology, processes, and people….

Establishing robust safeguards not only shields sensitive data but also cements a company’s reputation, fostering enduring relationships with clients. Every…

Securing APIs in business applications involves a multi-layered approach that addresses potential vulnerabilities at every stage of development and deployment….
Every organization encounters an ever-growing influx of sensitive and operational information. Without a well-defined data retention framework, businesses may face…

Enterprises migrating critical workloads to the cloud demand a comprehensive approach to safeguard sensitive information from unauthorized infiltration. Effective strategies…

Insider data theft poses one of the most complex challenges in business security. When trusted team members or contractors misuse…

The shift toward hybrid work models has transformed the way organizations operate, blending in-office collaboration with remote productivity. This evolution…

Embarking on a comprehensive cybersecurity audit empowers businesses to uncover hidden risks and strengthen their digital defenses. By methodically examining…

Distributed Denial of Service (DDoS) attacks pose a growing threat to companies of all sizes, potentially halting operations, eroding customer…
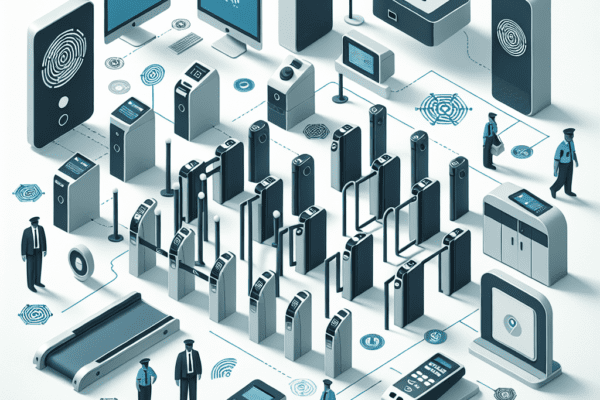
The role of physical access control in security is a critical aspect of safeguarding assets, information, and personnel within an…