
How to Create a Security-Focused Vendor Selection Process
Creating a robust, security-centered approach to vendor selection is essential for safeguarding sensitive data and ensuring operational resilience. A methodical,…

Creating a robust, security-centered approach to vendor selection is essential for safeguarding sensitive data and ensuring operational resilience. A methodical,…

Effective protection of organizational assets demands a comprehensive strategy for uncovering and addressing potential weaknesses. This article explores key approaches…

Embarking on a comprehensive cybersecurity audit empowers businesses to uncover hidden risks and strengthen their digital defenses. By methodically examining…

Managing the influx of connected devices in a corporate environment demands a strategic approach that goes beyond standard IT protocols….

The role of penetration testing in business security is crucial for identifying vulnerabilities and strengthening an organization’s defenses against cyber…
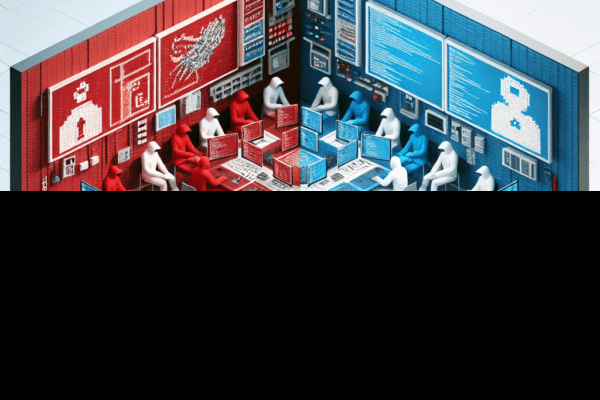
The importance of Red Team vs. Blue Team exercises cannot be overstated in the realm of business security. These exercises…