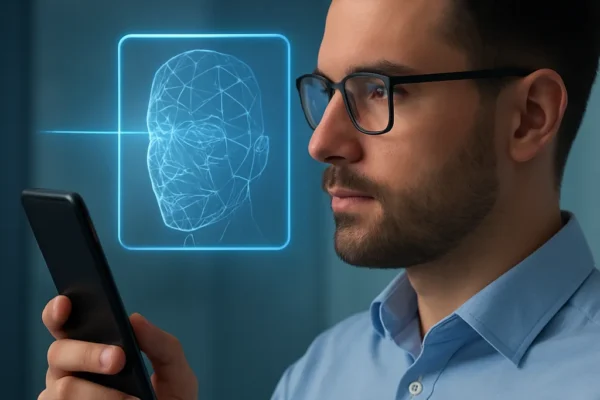
Why Continuous Authentication Is the Future of Security
Organizations today face a relentless onslaught of cyber threats, regulatory demands, and evolving workplace dynamics. Protecting sensitive data and ensuring…
Organizations today face a relentless onslaught of cyber threats, regulatory demands, and evolving workplace dynamics. Protecting sensitive data and ensuring…

Every minute of IT downtime quietly eats into revenue, reputation, and team morale. For many companies, a single failed PC…

Regular software updates are a fundamental aspect of maintaining robust security in any business environment. As technology evolves, so do…

Implementing a Bring Your Own Device (BYOD) security policy is essential for organizations looking to balance employee flexibility with the…