
How to Manage Data Privacy Across Multiple Jurisdictions
Managing data privacy in a landscape that spans multiple continents demands a strategic approach, blending legal insight, technical measures, and…

Managing data privacy in a landscape that spans multiple continents demands a strategic approach, blending legal insight, technical measures, and…

Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…

Protecting corporate information within Software-as-a-Service environments demands a strategic blend of policy, technology, and continuous vigilance. As organizations scale with…

As organizations expand their digital footprint, integrating robust security measures becomes indispensable to sustaining competitive advantage. Understanding cybersecurity not merely…
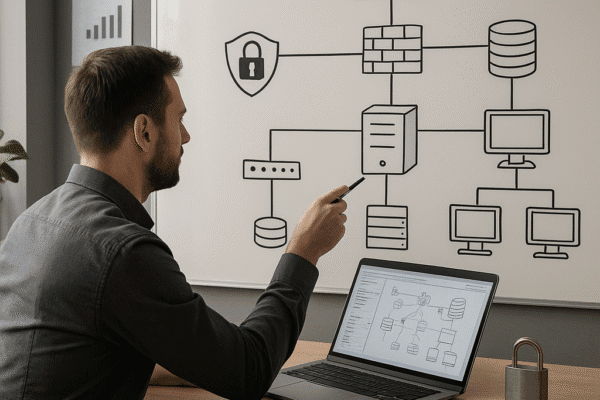
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

In a digital-first economy, uninterrupted access to accurate, secure, and compliant data has become a core condition for organizational survival….
Building a robust cybersecurity roadmap is essential for companies aiming to safeguard critical assets, ensure compliance, and maintain stakeholder trust….

Effective data encryption is a cornerstone of robust business security strategies, ensuring that sensitive information remains protected from unauthorized access….

Businesses increasingly rely on employees accessing corporate resources from their own smartphones, tablets, and laptops. Balancing convenience with the imperative…

Managing access for a distributed team requires a strategic approach that balances usability with ironclad protection. As organizations embrace flexible…