
The Importance of Multi-Factor Authentication for Businesses
Businesses around the globe face an escalating array of digital threats that demand robust solutions to safeguard sensitive information. Implementing…

Businesses around the globe face an escalating array of digital threats that demand robust solutions to safeguard sensitive information. Implementing…

Managing the integrity of a supply chain requires more than logistical coordination; it demands a strategic approach to cybersecurity that…

As organizations expand their distributed workforce, the challenge of safeguarding critical assets intensifies. Remote teams require a robust framework to…

The relentless advancement of cyber threats has compelled enterprises to rethink traditional perimeter defenses, propelling Zero Trust Architecture into the…

In an era defined by digital transformation and remote collaboration, businesses face a rapidly evolving threat landscape. As organizations expand…

Designing a secure office layout is essential for protecting both physical assets and sensitive information within a business environment. A…

Ensuring security in video conferencing platforms is crucial for businesses that rely on virtual communication. As remote work becomes increasingly…

Preventing unauthorized access to business systems is a critical aspect of maintaining the integrity, confidentiality, and availability of sensitive information….
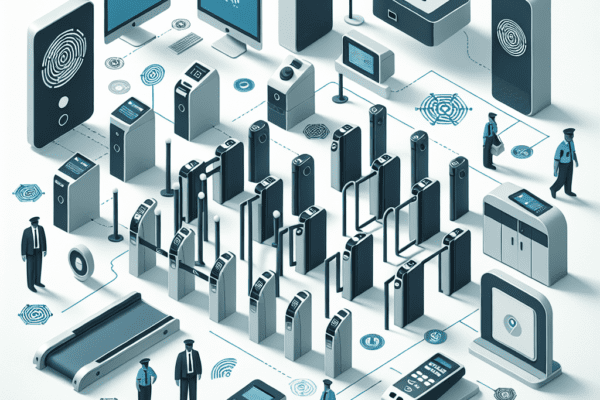
The role of physical access control in security is a critical aspect of safeguarding assets, information, and personnel within an…

Securing business IoT devices is a critical concern for organizations looking to leverage the benefits of connected technology while minimizing…