
How to Detect Unauthorized Devices on Your Network
Effective network security demands a proactive approach to identifying and neutralizing threats before they can compromise critical systems. Unauthorized devices…

Effective network security demands a proactive approach to identifying and neutralizing threats before they can compromise critical systems. Unauthorized devices…

Effective management of cyber incidents demands not only technical expertise but also a robust communication framework that guides organizations through…

Digital payment systems have revolutionized the way businesses and consumers exchange value, enabling swift transactions across borders and devices. However,…
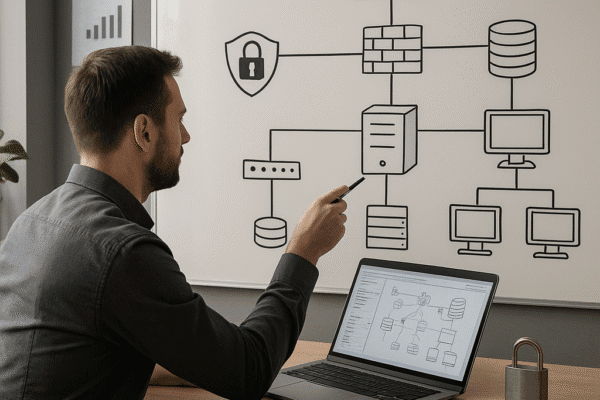
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

Managing security incidents that involve external vendors and suppliers demands a proactive and systematic approach. Organizations must weave rigorous processes…

Protecting a company from malicious actors targeting its supply chain demands a strategic blend of foresight, technical safeguards, and collaborative…

The allocation of resources for cybersecurity initiatives demands a clear demonstration of value to stakeholders. Organizations must navigate budget constraints…

Effective security oversight is critical for organizations aiming to safeguard assets, maintain trust, and sustain growth. By adopting regular security…

Effective password management is a cornerstone of a strong corporate security posture. Protecting sensitive data and preventing unauthorized access requires…
The Rise of quantum computing has sparked a profound shift in the digital landscape, challenging traditional notions of security and…