Why Continuous Authentication Is the Future of Security
Organizations today face a relentless onslaught of cyber threats, regulatory demands, and evolving workplace dynamics. Protecting sensitive data and ensuring…
Organizations today face a relentless onslaught of cyber threats, regulatory demands, and evolving workplace dynamics. Protecting sensitive data and ensuring…

Effective password management is a cornerstone of a strong corporate security posture. Protecting sensitive data and preventing unauthorized access requires…

The explosive growth of online marketplaces has elevated security concerns for digital storefronts. E-commerce businesses now face a complex array…

Protecting valuable creations from unauthorized access and exploitation requires a comprehensive, multi-layered approach that balances technology, process, and people. Organizations…

Protecting an organization’s sensitive access data requires a proactive stance and a blend of technical measures, human-centric strategies, and continuous…
The role of data masking in business security is increasingly vital as organizations strive to protect sensitive information while maintaining…

Preventing unauthorized access to business systems is a critical aspect of maintaining the integrity, confidentiality, and availability of sensitive information….
How to Safeguard Business Data During Employee Offboarding is a critical concern for organizations aiming to protect their sensitive information….
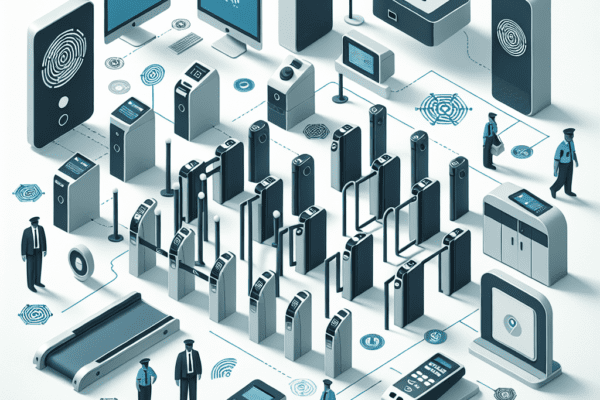
The role of physical access control in security is a critical aspect of safeguarding assets, information, and personnel within an…

Preventing business espionage is a critical concern for organizations aiming to protect their sensitive information and maintain a competitive edge….