
How to Establish a Cybersecurity Risk Register
Building a comprehensive risk register is a cornerstone of effective business security. A well-constructed register serves as both a strategic…

Building a comprehensive risk register is a cornerstone of effective business security. A well-constructed register serves as both a strategic…

Securing corporate databases requires more than basic measures; it demands a comprehensive strategy combining risk assessment, technical controls, and ongoing…

In the fast-paced world of corporate defense, organizations are constantly challenged by evolving threats. Leveraging threat intelligence effectively is no…

Creating an effective security awareness campaign demands a structured approach that engages employees, reinforces best practices, and fosters a culture…

Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…
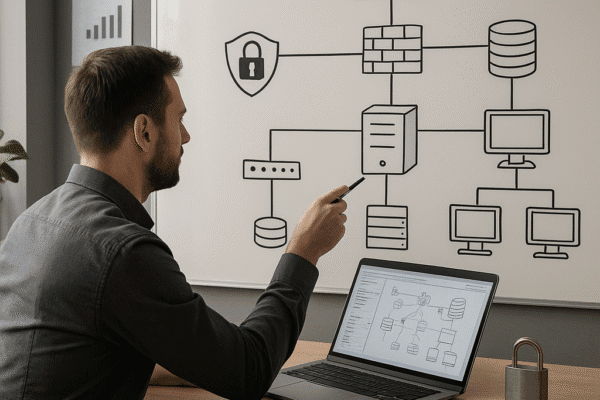
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

Managing security incidents that involve external vendors and suppliers demands a proactive and systematic approach. Organizations must weave rigorous processes…

Protecting a company from malicious actors targeting its supply chain demands a strategic blend of foresight, technical safeguards, and collaborative…

Mergers and acquisitions transform corporate structures, creating opportunities for growth and innovation while also exposing organizations to heightened cyber threats….

Continuous penetration testing is emerging as a cornerstone of modern business security strategies. By simulating adversarial techniques on a frequent…