
How to Prevent Account Takeover Attacks
Account takeover attacks represent one of the most insidious threats to modern organizations, targeting the very heart of corporate identity…

Account takeover attacks represent one of the most insidious threats to modern organizations, targeting the very heart of corporate identity…

Managing data privacy in a landscape that spans multiple continents demands a strategic approach, blending legal insight, technical measures, and…

Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…

Preparing for a regulatory cybersecurity inspection can feel like navigating a complex maze, but with the right strategy and disciplined…

As organizations expand their digital footprint, maintaining a robust security framework requires ongoing vigilance. A critical component of this framework…

Protecting corporate information within Software-as-a-Service environments demands a strategic blend of policy, technology, and continuous vigilance. As organizations scale with…

As organizations expand their digital footprint, integrating robust security measures becomes indispensable to sustaining competitive advantage. Understanding cybersecurity not merely…
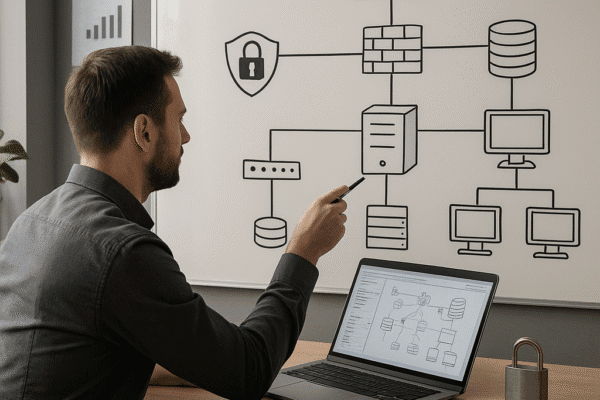
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

Containerization has transformed how organizations deliver and scale applications, but with great flexibility comes elevated risk. Securing these environments demands…

Building true resilience in today’s digital economy demands a systematic approach to measuring and improving your organization’s capacity to withstand,…