
How to Protect Business Data in SaaS Applications
Protecting corporate information within Software-as-a-Service environments demands a strategic blend of policy, technology, and continuous vigilance. As organizations scale with…

Protecting corporate information within Software-as-a-Service environments demands a strategic blend of policy, technology, and continuous vigilance. As organizations scale with…

As organizations expand their digital footprint, integrating robust security measures becomes indispensable to sustaining competitive advantage. Understanding cybersecurity not merely…
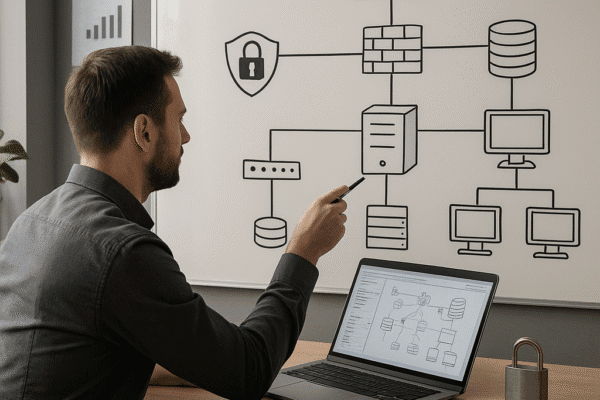
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

Containerization has transformed how organizations deliver and scale applications, but with great flexibility comes elevated risk. Securing these environments demands…

Building true resilience in today’s digital economy demands a systematic approach to measuring and improving your organization’s capacity to withstand,…

Behavioral analytics has emerged as a decisive approach to strengthening enterprise cybersecurity by emphasizing patterns of user activity rather than…

Effective collaboration often hinges on the seamless exchange of sensitive data between companies. Protecting these exchanges requires a multi-layered approach,…

Managing security incidents that involve external vendors and suppliers demands a proactive and systematic approach. Organizations must weave rigorous processes…
Every enterprise that relies on digital operations understands the gravity of safeguarding user access and maintaining trust. Early detection of…
Building a robust cybersecurity roadmap is essential for companies aiming to safeguard critical assets, ensure compliance, and maintain stakeholder trust….