
How to Protect Business Data from Physical Theft
Protecting business data from unauthorized access is a critical component of any comprehensive security strategy. Physical theft of servers, laptops,…

Protecting business data from unauthorized access is a critical component of any comprehensive security strategy. Physical theft of servers, laptops,…
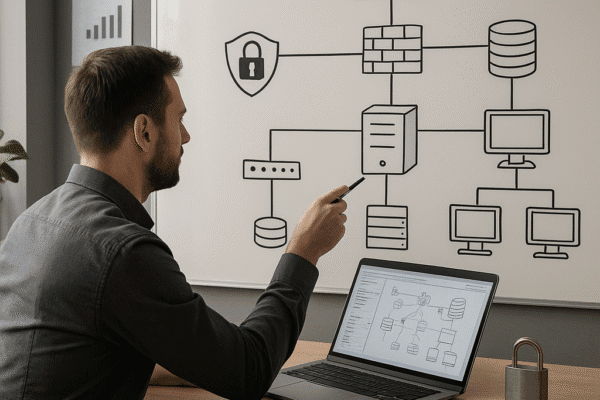
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

The digital frontier continues to evolve, bringing both unprecedented opportunities and novel threats to businesses of every scale. By embedding…

Establishing a robust framework for organizational safety requires a comprehensive security policy that aligns with business objectives and regulatory demands….

Securing highly sensitive financial transactions demands a comprehensive strategy that spans risk assessment, advanced encryption techniques, robust authentication protocols, and…

Protecting sensitive information is a critical aspect of modern business operations. Data leakage can undermine a company’s reputation, financial stability,…

Effective access control is at the heart of any comprehensive business security strategy. Organizations that fail to implement strong and…
Shadow IT represents the proliferation of unsanctioned software and hardware solutions within an organization. While often driven by employees’ pursuit…

Protecting a company’s sensitive information is not merely an IT concern; it is a critical aspect of overall business security….

Managing the influx of connected devices in a corporate environment demands a strategic approach that goes beyond standard IT protocols….