
How to Prevent Unauthorized Data Exfiltration
Protecting sensitive company information from unauthorized removal is a paramount concern for modern organizations. This article examines effective methods to…

Protecting sensitive company information from unauthorized removal is a paramount concern for modern organizations. This article examines effective methods to…

For any organization handling sensitive data, protecting communications from interception is crucial. Man-in-the-Middle attacks pose a significant threat to business…

Protecting business data from unauthorized access is a critical component of any comprehensive security strategy. Physical theft of servers, laptops,…

Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…
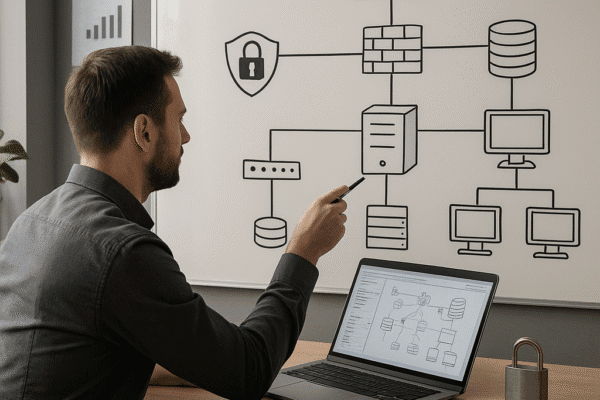
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

Businesses increasingly rely on employees accessing corporate resources from their own smartphones, tablets, and laptops. Balancing convenience with the imperative…

Managing access for a distributed team requires a strategic approach that balances usability with ironclad protection. As organizations embrace flexible…

The digital frontier continues to evolve, bringing both unprecedented opportunities and novel threats to businesses of every scale. By embedding…

Establishing a robust framework for organizational safety requires a comprehensive security policy that aligns with business objectives and regulatory demands….

The surge of interconnected systems and rapid adoption of cloud solutions demand a robust approach to protect valuable assets and…