
How to Protect Business Data in SaaS Applications
Protecting corporate information within Software-as-a-Service environments demands a strategic blend of policy, technology, and continuous vigilance. As organizations scale with…

Protecting corporate information within Software-as-a-Service environments demands a strategic blend of policy, technology, and continuous vigilance. As organizations scale with…
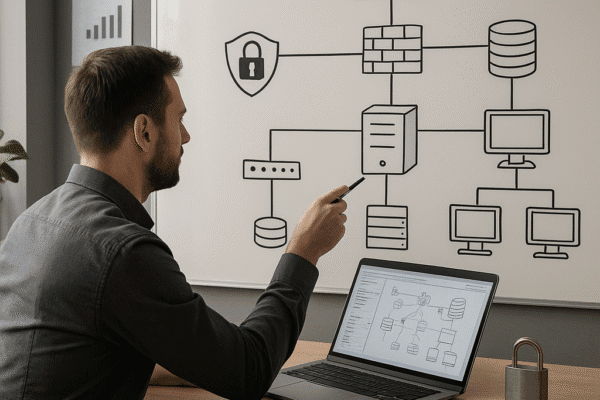
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…
Every enterprise that relies on digital operations understands the gravity of safeguarding user access and maintaining trust. Early detection of…
The Role of Threat Hunting in Modern Security Operations explores how organizations are shifting from reactive defense to a more…

The digital frontier continues to evolve, bringing both unprecedented opportunities and novel threats to businesses of every scale. By embedding…

Building an organization capable of withstanding and recovering from cyberattacks hinges on a strategic blend of technology, processes, and people….

In the realm of modern business security, organizations face a relentless barrage of sophisticated threats that evolve faster than traditional…

In the complex ecosystem of the internet, the Dark Web represents a hidden layer where access, activity, and content remain…

As businesses expand their digital footprint, maintaining robust security measures becomes a critical component of long-term success. Successfully navigating the…

The concept of threat intelligence has become an indispensable element in the arsenal of modern enterprises battling increasingly sophisticated digital…