
How to Improve Security Through Network Segmentation
Network segmentation offers a powerful approach to isolating threats, limiting the lateral movement of attackers, and reinforcing overall business security….

Network segmentation offers a powerful approach to isolating threats, limiting the lateral movement of attackers, and reinforcing overall business security….

Video conferencing platforms have become essential for seamless collaboration across distributed teams, but they also introduce a range of **privacy**…

Protecting modern assets demands a blend of strategic foresight, cutting-edge technology, and a culture of continuous improvement. Organizations tasked with…

Sharing sensitive information with external partners can boost efficiency and innovation, but it also introduces significant security challenges. Ensuring that…

The healthcare sector faces unique challenges when it comes to protecting sensitive patient data, maintaining operational integrity, and ensuring uninterrupted…

Protecting sensitive company information from unauthorized removal is a paramount concern for modern organizations. This article examines effective methods to…

Organizations often face the daunting task of safeguarding aging infrastructure while striving to remain competitive in a dynamic marketplace. Securing…
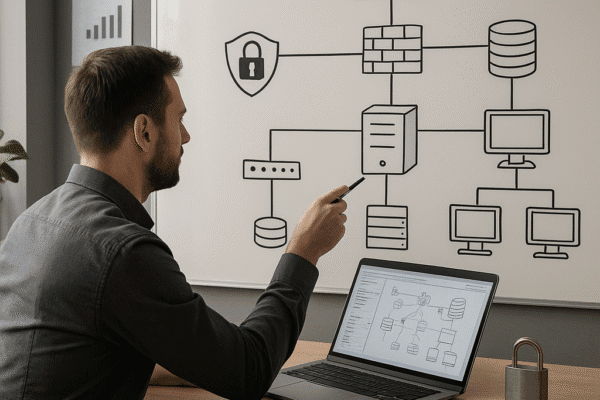
Designing a secure IT infrastructure is critical for businesses seeking to protect digital assets, maintain customer trust, and comply with…

In the competitive world of modern business, defending your organization from cunning adversaries requires a balanced blend of human vigilance,…

The digital frontier continues to evolve, bringing both unprecedented opportunities and novel threats to businesses of every scale. By embedding…